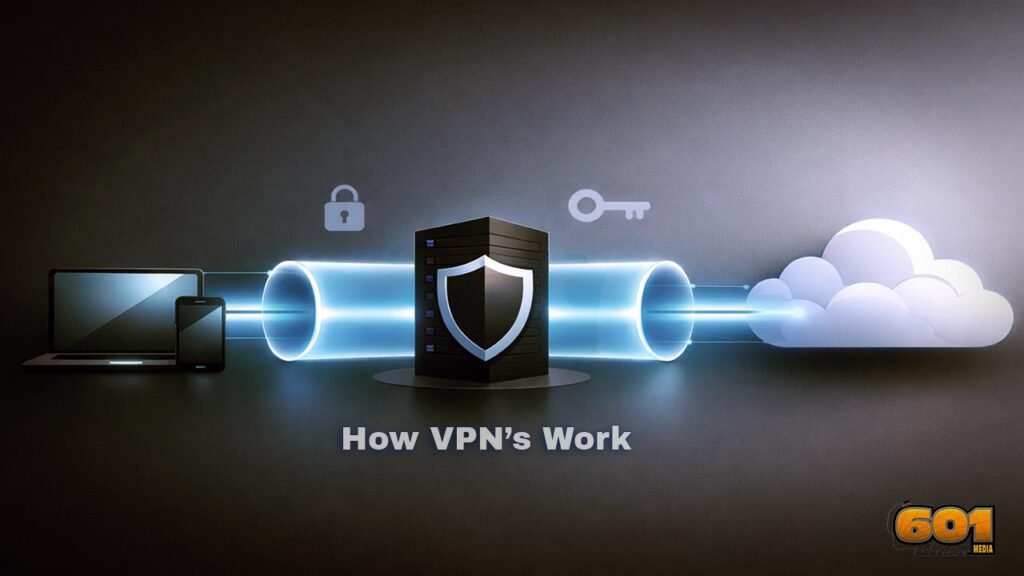
How VPNs Work
How VPNs Work: Security, Encryption, and Use Cases A VPN (Virtual Private Network) creates an encrypted “tunnel” between your device and a VPN server, reducing eavesdropping risk on untrusted networks, masking your IP address from the sites you visit, and enabling secure access to private resources. This article breaks down the moving parts—protocols, encryption, authentication, […]